Today we are excited to announce the preview of Palo Alto Networks Cloud Next Generation Firewall (NGFW) for Azure, available as a software as a service (SaaS) offering in Azure Virtual WAN. Azure Virtual WAN (vWAN), networking as a service brings networking, security, and routing functionalities together to simplify networking in Azure. With ease of use and simplicity built in, vWAN is a one-stop shop to connect, protect, route traffic, and monitor your wide area network.
Virtual WAN’s deep integration with the Palo Alto Networks managed firewall service allows you to enjoy the simplicity of a SaaS security offering without the hassles of managing provisioning, scaling, resiliency, software updates, or routing. A SaaS model enables a customer to deploy a solution by simply supplying necessary parameters and abstracting themselves from the management of network virtual appliances.
In this blog, we will focus on the Virtual WAN use case, followed by a brief overview of the behind-the-scenes secret sauce that makes it happen, and then understanding key Palo Alto Networks differentiating features.
The use case
Customers of Azure Virtual WAN can now use Palo Alto Networks Cloud NGFW for Azure to secure their traffic through their Virtual WAN deployments.
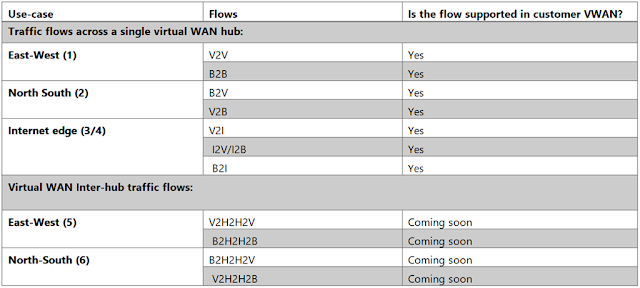
The different traffic flows that are supported by a customer’s vWAN deployment are illustrated below. Flows are numbered in the table below with the following assumptions:
◉ ‘B’ stands for a Branch which is a customer’s on-premises network connected to Azure through ExpressRoute circuits, Branch/Site-to-site VPN, or Remote user/Point-to-site connections.
◉ ‘V’ stands for VNet—Azure Virtual networks hosting customer services and connected to a Virtual WAN hub. It may also be referred to as spoke VNet.
◉ ‘I’ stands for internet, which means the customer traffic that originates from or terminates in the internet and traverses through Azure Virtual WAN.
◉ ‘H’ stands for Azure Virtual hub.
◉ Traffic flows across a single hub are traffic flows originating and terminating on endpoints connected to the same virtual hub. These may also be referred to as Intra-hub flows.
◉ Inter-hub flows are traffic flows that traverse across 2 virtual hubs to get to the destination.
Figure 1: Supported use case and traffic flows in Azure Virtual WAN with Palo Alto Networks Cloud NGFW.
User experience
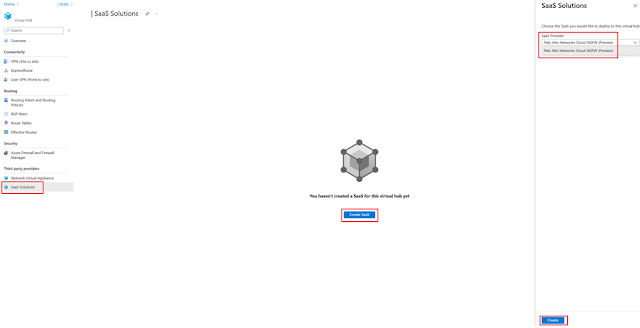
Customers can add Palo Alto Networks Cloud NGFW to an Azure Virtual WAN Hub in the Azure portal. After a hub is created, click on the hub name and navigate to Third-party Providers -> SaaS solutions –> Create SaaS and choose the Palo Alto Networks Cloud NGFW option.
Figure 2: Discover Palo Alto Networks Cloud NGFW.
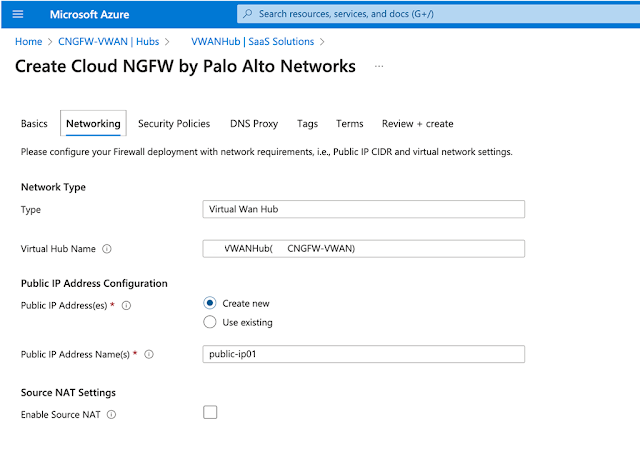
After clicking “Create”, you’ll be taken to a wizard experience where you can configure and customize your Cloud NGFW SaaS deployment. You can customize key networking and security attributes of your SaaS such as selecting public Ips, DNS proxy settings, security policies, and security settings.
Figure 3: Create and set up security settings in Palo Alto Networks Cloud NGFW.
After the Cloud NGFW has been successfully provisioned, you can manage your SaaS Firewall by navigating to your Virtual Hub -> Third-party providers -> SaaS solutions -> Manage SaaS. Explore here for more information on available options.
How does this all work within Virtual WAN
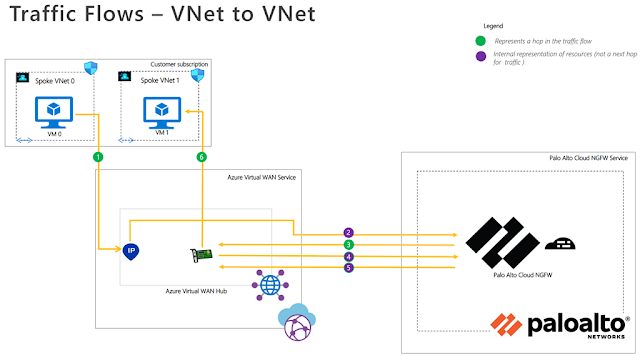
As mentioned in the prior section, Virtual WAN supports multiple flows. To illustrate the behind-the-scenes workings in Virtual WAN, we will use East-West (V2V) traffic flows.
Figure 4: Traffic flows within Virtual WAN for East-West (V2V) traffic to-fro Palo Alto Networks Cloud NGFW.
As you can see, the complexities of traffic engineering, and infrastructure management are completely removed and the user gets to just focus on securing the right security policies for their network traffic.
Key highlights of the Palo Alto Networks Cloud NGFW for Azure integration with Virtual WAN
Palo Alto Networks Cloud NGFW for Azure integrates with Azure Virtual WAN deployments, enabling customers to protect traffic across their entire network. While there are several cool and turn-key features built into the integration, a few that are worth calling out are below:
◉ Machine learning powered NGFW: Cloud NGFW for Azure uses AI and machine learning to detect and stop known, unknown, and zero-day threats, enabling customers to stay ahead of sophisticated adversaries.
◉ Consistent Security and Management from On-Premises to Azure: Cloud NGFW for Azure is integrated with Panorama, Palo Alto Networks policy management solution. The integration of Panorama with Cloud NGFW for Azure offers a host of benefits to customers. Firstly, it enables seamless security policy extension from on-prem to Azure, simplifying operations and reducing administrative workload and total cost of ownership. More importantly, this integration enforces the same high standards of security in the cloud, ensuring that customers’ cloud environments are secure and protected against cyber threats. Additionally, the integration provides centralized visibility, providing valuable insights into the threats on their network enabling customers to manage their security policies through their existing Panorama console, streamlining management, allowing their cloud teams to focus on application migration and new application development.
◉ Ease of use: Palo Alto Networks Cloud NGFW is designed to be incredibly easy to use. Similar to Virtual WAN product principles for simplicity and ease of use, this Palo Alto Networks integrated solution allows customers to procure and deploy the solution directly from the Azure portal in just a few minutes, providing instant protection against cyber threats. The solution is also painless to operate as Palo Alto Networks takes care of scaling, resilience, and software updates. This integration gives customers the agility and flexibility they need to manage their cloud security while focusing on their core business objectives.
Source: microsoft.com





0 comments:
Post a Comment