To ensure customers running on Azure are protected against ransomware attacks, Microsoft has invested heavily in Azure security and has provided customers with the security controls needed to protect their Azure cloud workloads.
A comprehensive overview of best practices and recommendations can be found in the "Azure Defenses for Ransomware Attack" e-book.
Here, we would like to zoom into network security and understand how Azure Firewall can assist you with protecting against ransomware.
Ransomware is basically a type of malicious software designed to block access to your computer system until a sum of money is paid. The attacker usually exploits an existing vulnerability in your system to penetrate your network and execute the malicious software on the target host.
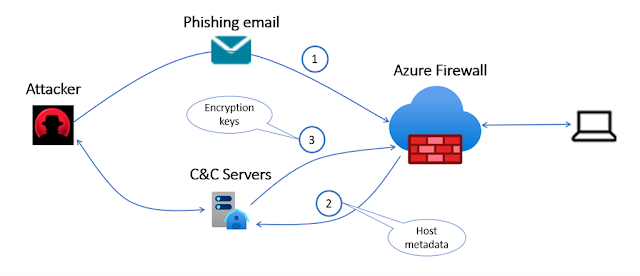
Ransomware is often spread through phishing emails that contain malicious attachments or through drive-by downloading. Drive-by downloading occurs when a user unknowingly visits an infected website and then malware is downloaded and installed without the user’s knowledge.
Here Azure Firewall Premium comes into help. With its intrusion detection and prevention system (IDPS) capability, every packet will be inspected thoroughly, including all its headers and payload to identify malicious activity and to prevent it from penetrating your network. IDPS allows you to monitor your network for malicious activity, log information about this activity, report it, and optionally attempt to block it.
The IDPS signatures are applicable for both application and network-level traffic (Layers 4-7), they are fully managed and contain more than 65,000 signatures in over 50 different categories to keep them up to date with the dynamic ever-changing attack landscape:
1. Azure Firewall is getting early access to vulnerability information from Microsoft Active Protections Program (MAPP) and Microsoft Security Response Center (MSRC).
2. Azure Firewall is releasing 30 to 50 new signatures each day.
Nowadays, modern encryption, such as Secure Sockets Layer (SSL) or Transport Layer Security (TLS), is used globally to secure internet traffic. Attackers are using encryption to carry their malicious software into the victim network. Therefore, customers must inspect their encrypted traffic just like any other traffic.
Azure Firewall Premium IDPS allows you to detect attacks in all ports and protocols for non-encrypted traffic. However, when HTTPS traffic needs to be inspected, Azure Firewall can use its TLS inspection capability to decrypt the traffic and accurately detect malicious activities.
After the ransomware is installed on the target machine, it may try to encrypt the machine’s data, therefore it requires using an encryption key and may use the Command and Control (C&C) to get the encryption key from the C&C server hosted by the attacker. CryptoLocker, WannaCry, TeslaCrypt, Cerber, and Locky are some of the ransomware using C&C to fetch the required encryption keys.
Azure Firewall Premium has hundreds of signatures that are designed to detect C&C connectivity and block it to prevent the attacker from encrypting customers’ data.





0 comments:
Post a Comment